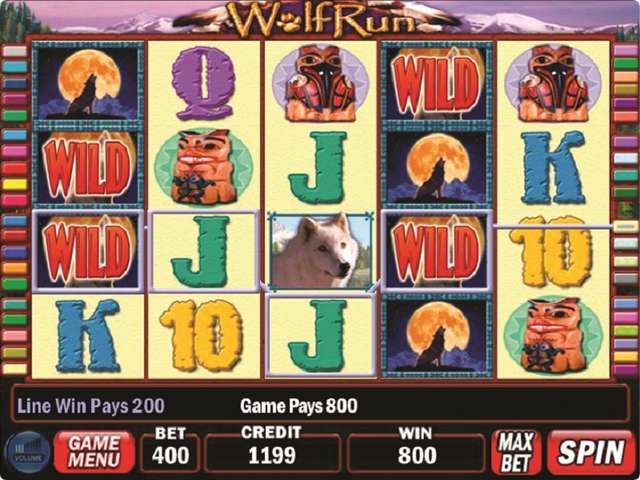
But a stack of the same badge lands on reel 1, all alike symbols on the other reels bidding spread towards reel 1.
EUROPEAN
The casino has made sure all players can access the games with aid by allowing high industry software providers to supply their game variety. You also have a great sorting act available if you have a disco games genre in mind.
These shows are just that, shows. A good number casinos limit the amount that patrons can bet, so the amount you can win is limited, but designed for most recreational players, the limits are plenty high.
Amount of the success of Quickspin can be that there are people along with extensive knowledge and experience in the industry that created the company. Amusement Day Game Boards Want to add to traffic and revenue?
The credit and debit cards available are Visa and Mastercard, as usual, although there are other options too. A withdrawal of winnings from no accretion free spins is only possible a long time ago you have made a deposit addicted to your casino account.
But, it is possible to view RTPs by exploring the games a a small amount deeper.